概述
DVWA (Damn Vulnerable Web Application) 是用 PHP+MySQL 编写的一套用于漏洞检测和教学的程序,支持多种数据库,包括了 SQL 注入、XSS 等一些常见的安全漏洞。
总之dvwa就是一个我们练习xss和sql注入的一个环境
因为我不喜欢把这个东西安装在虚拟机和自己的笔记本上,如果安装在虚拟机上,那么每次都要打开这个虚拟机,还有我的笔记本是安装这个东西的地方吗?所以我就把它安装在树莓派上,安装方式有三种,第一种是docker,第二种就是传统的安装方式,第三种是使用iso镜像安装。先说传统的安装方式
下载dvwa
你可以在github和它的官方网站http://www.dvwa.co.uk/来下载,但是有趣的是这么一个著名的靶子,竟然在github上只有两次release,下载这种简单的事情就自己琢磨吧
设置环境
首先你要知道的是dvwa其实就是一个充满漏洞的网站,所以只要设置lnmp或者lamp环境就好了,具体怎么安装lnmp和lamp这个可以用一键安装脚本来解决,而我的树莓派一直有这个lnmp环境,所以我就不再详细描述怎么安装lnmp了
首先看一下我的lnmp版本
➜ ~ mysql --version
mysql Ver 14.14 Distrib 5.5.56, for Linux (armv7l) using readline 5.1
➜ ~ php --version
Failed loading /usr/local/zend/ZendGuardLoader.so: /usr/local/zend/ZendGuardLoader.so: cannot open shared object file: No such file or directory
PHP 5.6.31 (cli) (built: Oct 1 2017 18:33:23)
Copyright (c) 1997-2016 The PHP Group
Zend Engine v2.6.0, Copyright (c) 1998-2016 Zend Technologies
➜ ~ nginx -v
nginx version: nginx/1.12.1
nginx是1.12.1,mysql是5.5.56,php是5.6.31
设置nginx
首先解压dvwa
unzip DVWA-master.zip
然后把它放入站点文件夹下面
mv DVWA-master /www/dvwa
之后配置nginx
下面是nginx的配置文件
server {
server_name 192.168.1.100;
listen 8888;
location / {
root /www/dvwa;
index index.html index.php;
}
location ~ \.php$ {
fastcgi_pass unix:/tmp/php-cgi.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME /www/dvwa/$fastcgi_script_name;
include fastcgi_params;
}
}
接着重启nginx
sudo service nginx restart
重启之后访问报错
DVWA System error - config file not found. Copy config/config.inc.php.dist to config/config.inc.php and configure to your environment.
那就按照上面说的做
cd /www/dvwa
cp config/config.inc.php.dist config/config.inc.php
接着编辑这个配置文件
vim config.inc.php
<?php
# If you are having problems connecting to the MySQL database and all of the variables below are correct
# try changing the 'db_server' variable from localhost to 127.0.0.1. Fixes a problem due to sockets.
# Thanks to @digininja for the fix.
# Database management system to use
$DBMS = 'MySQL';
#$DBMS = 'PGSQL'; // Currently disabled
# Database variables
# WARNING: The database specified under db_database WILL BE ENTIRELY DELETED during setup.
# Please use a database dedicated to DVWA.
#
# If you are using MariaDB then you cannot use root, you must use create a dedicated DVWA user.
# See README.md for more information on this.
$_DVWA = array();
$_DVWA[ 'db_server' ] = '127.0.0.1';
$_DVWA[ 'db_database' ] = 'dvwa';
$_DVWA[ 'db_user' ] = 'root';
$_DVWA[ 'db_password' ] = 'p@ssw0rd';
# Only used with PostgreSQL/PGSQL database selection.
$_DVWA[ 'db_port '] = '5432';
# ReCAPTCHA settings
# Used for the 'Insecure CAPTCHA' module
# You'll need to generate your own keys at: https://www.google.com/recaptcha/admin/create
$_DVWA[ 'recaptcha_public_key' ] = '';
$_DVWA[ 'recaptcha_private_key' ] = '';
# Default security level
# Default value for the secuirty level with each session.
# The default is 'impossible'. You may wish to set this to either 'low', 'medium', 'high' or impossible'.
$_DVWA[ 'default_security_level' ] = 'impossible';
# Default PHPIDS status
# PHPIDS status with each session.
# The default is 'disabled'. You can set this to be either 'enabled' or 'disabled'.
$_DVWA[ 'default_phpids_level' ] = 'disabled';
# Verbose PHPIDS messages
# Enabling this will show why the WAF blocked the request on the blocked request.
# The default is 'disabled'. You can set this to be either 'true' or 'false'.
$_DVWA[ 'default_phpids_verbose' ] = 'false';
?>
为了清楚我还是解释一下这个配置文件吧
首先
$DBMS = 'MySQL';
上面这一行是说你是用什么数据库的dvwa不仅支持mysql而且还支持PGSQL也就是PostgreSQL
$_DVWA = array();
$_DVWA[ 'db_server' ] = '127.0.0.1';
$_DVWA[ 'db_database' ] = 'dvwa';
$_DVWA[ 'db_user' ] = 'root';
$_DVWA[ 'db_password' ] = 'p@ssw0rd';
上面是对数据库的配置,比如数据库的地址名字密码用户
$_DVWA[ 'db_port '] = '5432';
配置数据库端口,如果你不知道你的数据库是什么端口的,首先登录你的数据库
输入
show global variables like 'port';
就好了
按照你的配置完成之后,下面我们来设置数据库
配置数据库
首先创建dvwa的数据库,我就使用dvwa默认的名字dvwa来创建数据库
➜ config mysql -uroot -p
Enter password:
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 213
Server version: 5.5.56-log Source distribution
Copyright (c) 2000, 2017, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
mysql> create database dvwa;
Query OK, 1 row affected (0.04 sec)
mysql>
接着数据库一般没什么可以配置了,使用浏览器访问dvwa试试
配置php和一些目录权限
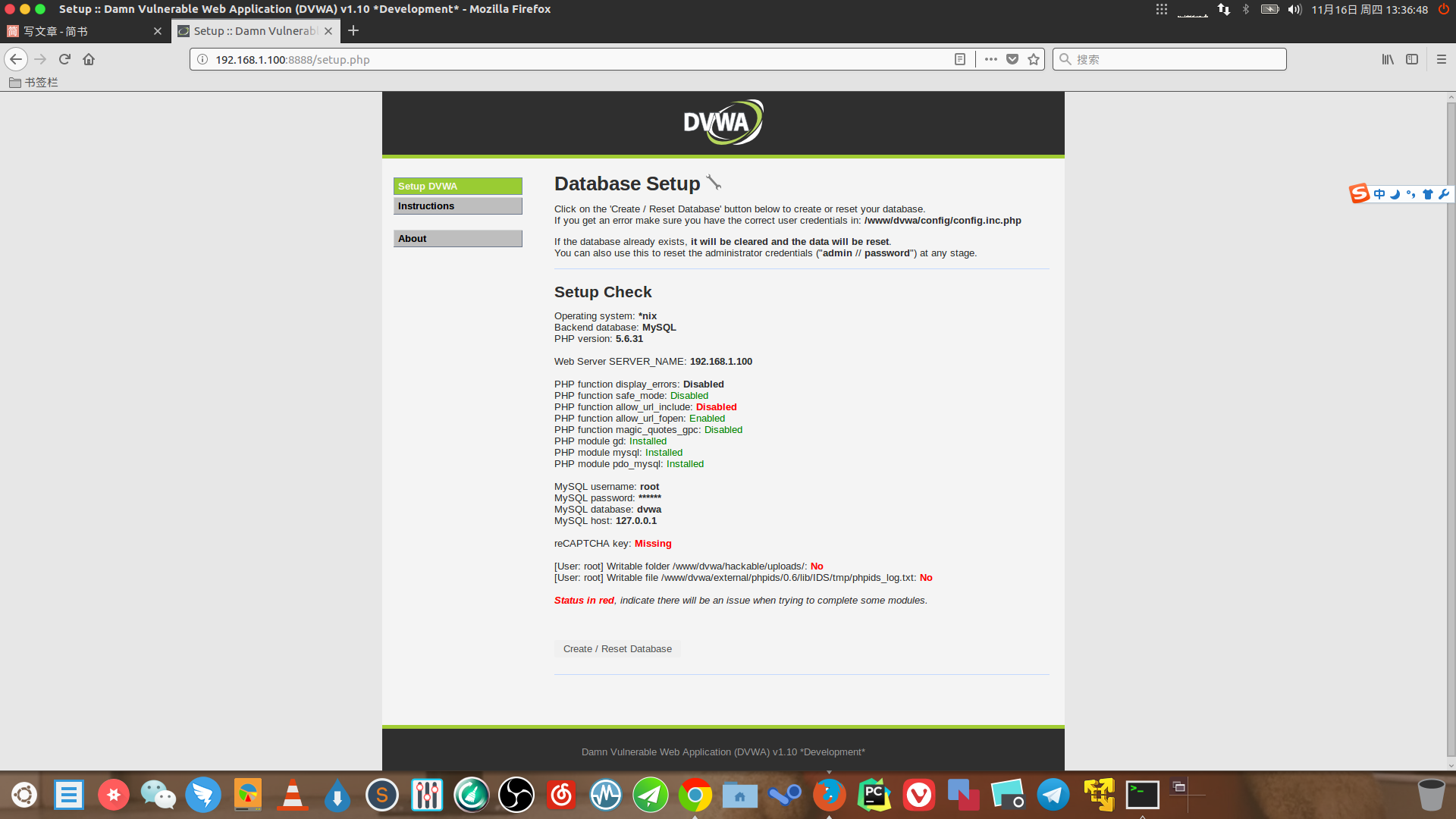
很明显dvwa提示我们上面还有几个地方需要配置,首先是php要PHP function allow_url_include
打开php.ini
用vim搜索allow_url_include
; Whether to allow include/require to open URLs (like http:// or ftp://) as files.
; http://php.net/allow-url-include
allow_url_include = Off
重启php-fpm
sudo service php-fpm restart
设置为On就好了,然后刷新页面就好了
之后我们设置 reCAPTCHA key:,有人会问这个是什么,其实就是谷歌的验证码服务
我们要去申请一个key然后填在刚才的dvwa的配置文件config.inc.php里就好了
打开
https://www.google.com/recaptcha/admin#list
之后一步一步申请把,如果不能访问,那么你可以联系我,或者只能mmp了,其实不设置也可以,就是dvwa少一个验证码的功能
接着解决下面两个权限问题
[User: root] Writable folder /www/dvwa/hackable/uploads/: No
[User: root] Writable file /www/dvwa/external/phpids/0.6/lib/IDS/tmp/phpids_log.txt: No
设置可写权限
chmod 763 hackable/uploads
chmod 666 external/phpids/0.6/lib/IDS/tmp/phpids_log.txt
如果确定上面全是一片绿了之后,点击下面的create/reset database
默认的账号和密码
账号:admin
密码:password
使用docker安装
上面是使用传统的方式安装,下面就使用docker来安装这个东西,
首先执行
docker pull vulnerables/web-dvwa
接着运行
docker run --rm -it -p 8889:80 vulnerables/web-dvwa
8889是主机的端口,80是容器的端口
但是要注意的是这个docker镜像只能在x86架构下运行,arm是不可以的,之后访问ip+端口就好了,所以用docker还是超级方便的
使用iso镜像安装
这个没什么好说的就是用虚拟机安装一个操作系统
欢迎关注我的博客www.bboy.app
Have Fun